JWT (JSON Web Token): A Secure and Flexible Approach to Authentication
In today's interconnected digital landscape, secure authentication mechanisms are paramount to safeguarding user data and maintaining trust in web applications. JSON Web Token (JWT) has emerged as a popular and efficient method for achieving secure authentication and authorization. In this blog post, we will explore the concept of JWT, its structure, working principle, and its significance in modern web development.
Table of Contents:
What is JWT?
Anatomy of a JWT
How JWT Works
Advantages of JWT
Practical Applications
Conclusion
1. What is JWT?
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way of transmitting information between parties as a JSON object. It is commonly used to securely transmit information between a client (typically a web browser) and a server, providing a trusted form of authentication and authorization.
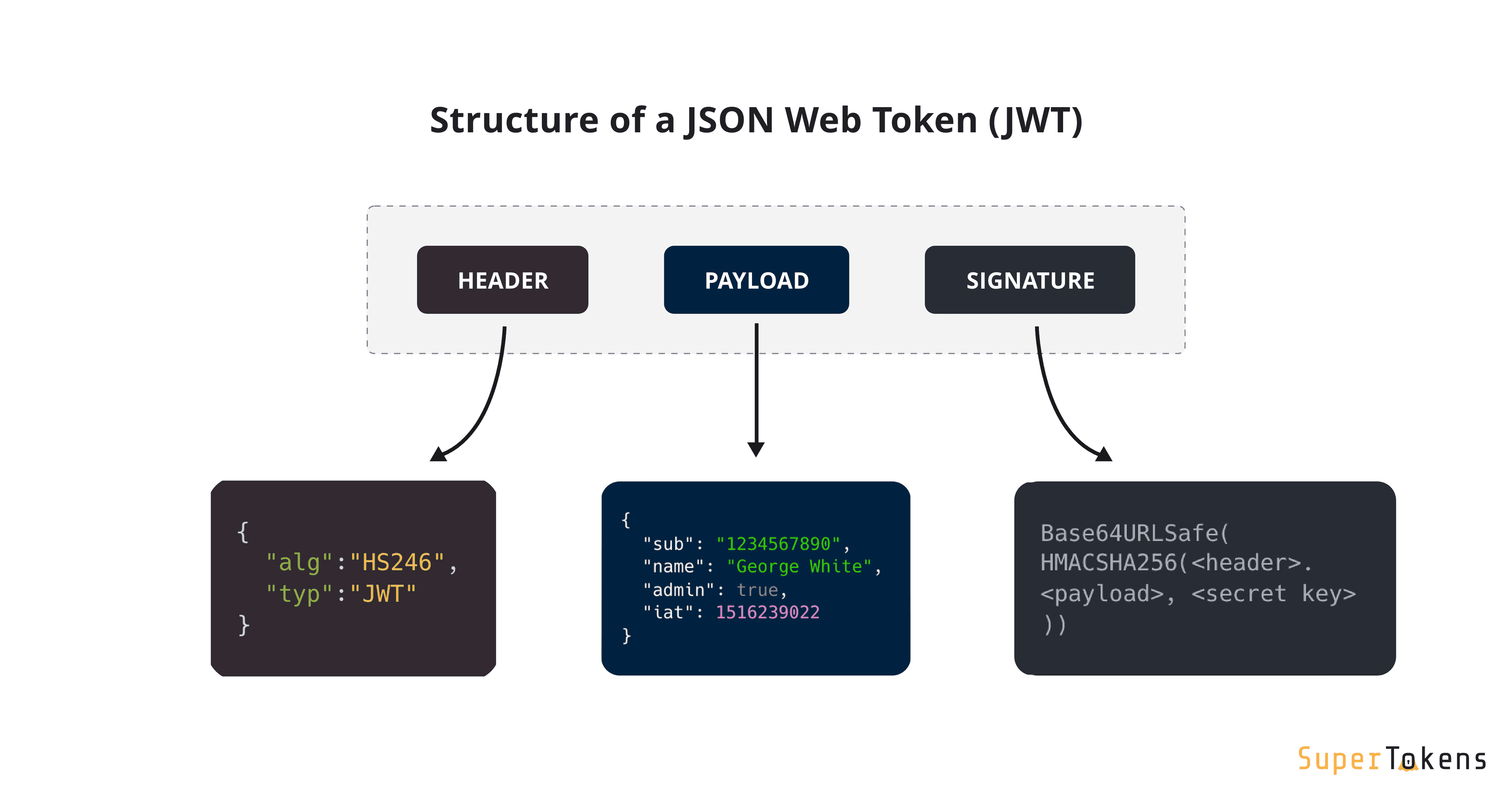
2. Anatomy of a JWT:
A JWT is composed of three parts separated by dots ('.'): Header, Payload, and Signature.
header.payload.signature
- Header: The header typically consists of two parts: the type of token (JWT) and the signing algorithm used, such as HMAC SHA256 or RSA.
{
"alg": "HS256",
"typ": "JWT"
}
- Payload: The payload contains the claims (statements) about the user and additional data. Claims are classified as registered, public, and private claims.
{
"sub": "1234567890",
"name": "John Doe",
"admin": true
}
- Signature: To create the signature part, the encoded header, encoded payload, and a secret key are used. The signature ensures the integrity of the token and can verify if it has been tampered with.
HMACSHA256(
base64UrlEncode(header) + "." +
base64UrlEncode(payload),
secretKey
)
3. How JWT Works:
The process of using JWT for authentication typically involves the following steps:
User Authentication: When a user logs in or provides authentication credentials, the server verifies the credentials and generates a JWT.
JWT Issuance: The server creates a JWT, comprising the user's identity and any additional claims, then signs it with a secret key. The JWT is sent back to the client.
JWT Usage: The client stores the JWT, typically in a cookie or local storage. For each subsequent request to the server, the client includes the JWT in the request headers.
JWT Validation: The server validates the JWT by verifying the signature and decoding the payload. If the JWT is valid and not expired, the server allows access to the requested resources.
4. Advantages of JWT:
JWT offers several advantages over traditional session-based authentication methods:
Stateless: Since JWTs are self-contained, servers do not need to maintain session data, making them stateless and highly scalable.
Security: JWTs are signed with a secret key, ensuring data integrity and preventing tampering. Additionally, they can be encrypted for an extra layer of security.
Flexibility: The payload allows for custom claims, making JWTs flexible and versatile for various application requirements.
5. Practical Applications:
JWT finds applications in various scenarios, including:
Single Sign-On (SSO): JWT allows users to log in once and access multiple applications without requiring multiple logins.
API Authentication: JWT is commonly used to authenticate API requests, providing a secure and straightforward way to protect sensitive endpoints.
Authorization: JWT's payload can include user roles and permissions, enabling fine-grained access control.
6. Conclusion:
JSON Web Token (JWT) has become a go-to method for secure and efficient authentication in modern web development. Its compactness, flexibility, and security features make it a preferred choice for developers and security experts alike.
By understanding the anatomy of a JWT and its working principle, developers can implement robust and reliable authentication mechanisms that enhance the security of their applications.
So, leverage the power of JWT to secure your applications and enable seamless user experiences while preserving data integrity and trust in your web ecosystem.
Happy coding with JWT!